Introduction: Why Secure SDLC Matters More Today Than Ever
If you search how to build secure SDLC right now, you’ll find thousands of checklists, buzzwords, and long theoretical models – but very few real, practical guides showing how teams actually implement it in the real world. And that’s the problem.
Security today is no longer a “nice-to-have.” It has become a survival requirement. Modern engineering teams ship faster than ever thanks to microservices, CI/CD, GitOps, low-code pipelines, and AI-assisted coding. But this speed also creates an enormous attack surface.
A Secure Software Development Life Cycle (SDLC) is no longer about sprinkling scanners into your pipeline. It’s about building security into the culture, the tools, the workflows, and the architecture itself.
This guide brings together:
- Real implementation insights
- Benchmarks from frameworks like OWASP SAMM, NIST SSDF, and ISO 27034
- Practical step-by-step instructions
- Recommendations you can adopt immediately
- Lessons from teams who built secure SDLCs from scratch
By the end, you’ll walk away with a clear blueprint for building a secure SDLC tailored to your engineering culture – not a generic security textbook.
The Foundation: What a Secure SDLC Actually Is
A Secure SDLC integrates security into every phase of software development:
| SDLC Phase | Key Security Activities |
|---|---|
| Planning | Threat modelling, risk ranking, data classification |
| Design | Security architecture, secure patterns, library selection |
| Development | SAST, SCA, IDE plugins, secure coding |
| Testing | DAST, IAST, security test cases, code reviews |
| Deployment | Secrets management, configuration hardening |
| Maintenance | Monitoring, incident response, patching |
A mature Secure SDLC ensures three things:
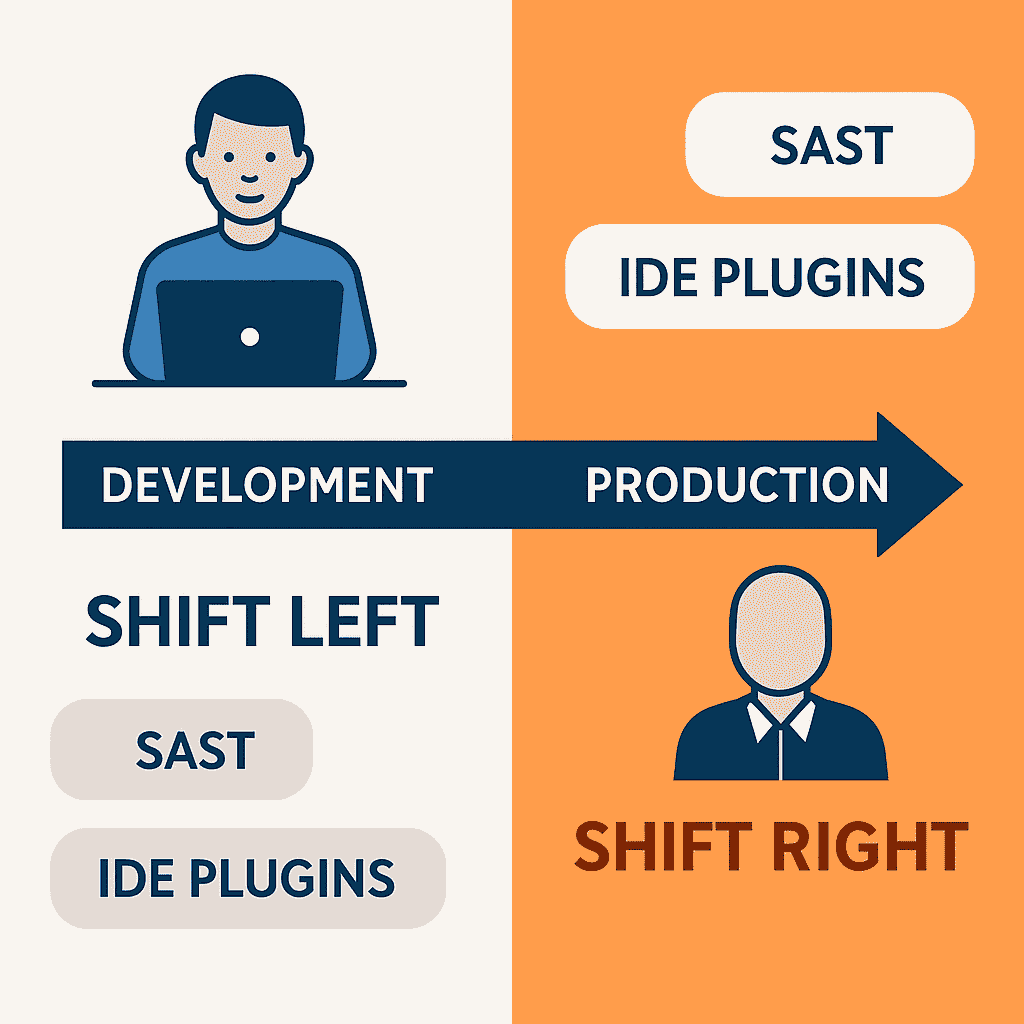
- Security shifts left into development: Developers detect issues while writing code, not after release.
- Controls shift right into production: Runtime protection complements left-shift controls.
- Security becomes measurable: Metrics guide improvements instead of guesswork.
Step 1: Establish the Vision, Principles & Governance
Before tools, scanners, or pipelines – define why you want a Secure SDLC. A strong Secure SDLC starts with a clear “north star”:
Security Vision Example: “Security should reduce friction, enable safe delivery, and scale across teams. It must be automated, predictable, and embedded into engineering culture.”
Core Principles to Adopt:
- Security = Quality
- Developers own security outcomes
- Automate everything repeatable
- Review anything involving risk
- Measure everything
Define Roles Early: A secure SDLC collapses without clarity on who does what.
| Role | Responsibility |
|---|---|
| Developers | Fix vulnerabilities, adopt secure patterns |
| AppSec Team | Build guardrails, perform reviews, govern frameworks |
| DevOps/Platform | Implement security automation |
| Product Owners | Risk acceptance, prioritization |
| Security Architects | Oversee cross-platform security patterns |
If the roles aren’t clear, everything becomes an argument. Clarifying them keeps your SDLC scalable.
Step 2: Perform a Baseline Assessment
Before building anything new, you must know where you stand. Use credible models such as:
- OWASP SAMM (highly practical)
- NIST SSDF (very compliant-friendly)
- BSIMM (industry benchmarked)
Assess:
- What controls exist today?
- What gaps are highest risk?
- What can be automated?
- Which teams are bottlenecks?
- What policies need rewriting?
Pro Tip: Avoid boiling the ocean: Start with 1-2 high-impact controls per SDLC phase, not 20 new tasks.
Step 3: Build & Deploy the Core Controls (Phase-by-Phase)
This is where your Secure SDLC takes shape.
PLANNING PHASE: Risk & Threat Modelling
Planning must never start with code – it starts with clarity. Implement:
- Lightweight threat modelling
- Data classification (what’s sensitive?)
- Initial abuse case identification
- Risk rating (based on OWASP Risk Rating or FAIR)
Tools to consider:
- Threat Dragon
- IriusRisk
- Miro-based threat modelling templates
Pro Tip: Don’t force 2-hour workshops every sprint. Adopt “Just-In-Time” threat modelling: A 10-minute conversation during grooming is often enough.
DESIGN PHASE: Architecture, Patterns & Guardrails
This phase is where most vulnerabilities originate – Insecure Design is again in the OWASP Top 10 (2025). Implement:
- Architecture review checklists
- Secure design patterns (e.g., OAuth, JWT, Input Validation Framework)
- Pre-approved libraries & frameworks
- Secure-by-default configuration templates
- Secrets design review (vaulting, rotation)
Secure design patterns prevent vulnerabilities like SSRF which often originate from architectural flaws. Create a reusable “Security Blueprint Library”:
- API design best practices
- Microservice trust boundaries
- Logging & observability patterns
- Token handling patterns
- Cloud service baselines
When developers follow blueprints, you remove ambiguity – and remove vulnerabilities.
DEVELOPMENT PHASE: Shifting Security Left
This is where SDLC success or failure becomes visible. Implement:
- SAST integrated into IDE (not only CI/CD)
- SCA for dependency security
- Pre-commit hooks
- Secure coding training mapped to your stack
- Developer-friendly remediation guidance
Developer Enablement Matters: Security should feel like a helper, not a blocker. Consider embedding:
- VS Code / JetBrains security plugins
- CodeQL queries tuned to your environment
- Semgrep custom rules for business logic checks
Pro Tip: Fix security findings in the same sprint, not months later. Long backlogs kill security culture.
TESTING PHASE: Validate What Matters
Security testing must be risk-driven, not endless checklists. Implement:
- DAST for runtime testing
- IAST for deep instrumentation
- Manual security code review
- Penetration testing (risk-based, not calendar-based)
- API security testing
Penetration testing in secure SDLC often reveals privilege escalation vectors that need immediate attention. Automated Security Test Cases examples:
- File upload bypass
- JWT token tampering
- CORS misconfigurations
- Broken Access Control (OWASP #1)
- SSRF checks
- SQLi & XSS auto-detection
- Authorization matrix testing
This phase catches what the left-shift controls miss.
DEPLOYMENT PHASE: Hardening & Release Security
A secure SDLC must ensure that “secure code” is deployed into a “secure environment.” Implement:
- Secrets scanning
- Container image scanning
- IaC scanning (Terraform, CloudFormation)
- Configuration policies (Open Policy Agent)
- GitOps security checks
Just as DNS security protects your infrastructure in production, a secure SDLC protects your applications from development.
Release Gates – Define simple criteria:
| Gate | Requirement |
|---|---|
| Critical vulnerabilities | Must be fixed |
| High vulnerabilities | Fix or raise risk acceptance |
| Medium/Low | Added to backlog with SLA |
| Secrets in code | Block release |
| Missing logs/monitoring | Block release for high-risk apps |
A release pipeline with clear gates builds trust across teams.
MAINTENANCE PHASE: Keep Security Alive
Security doesn’t end at deployment. Implement:
- Continuous monitoring (SIEM, WAF, RASP, API firewalls)
- Automated patching
- Vulnerability management SLAs
- Incident response runbooks
- Annual red-team exercises
- Regular Secure SDLC reviews
Continuous monitoring in secure SDLC is similar to DNS leak monitoring for ongoing protection. Why this phase matters: Most breaches happen long after an app goes live – when no one is watching. This phase ensures security never “fades away.”
Step 4: Integrate Everything into CI/CD (Automation Layer)
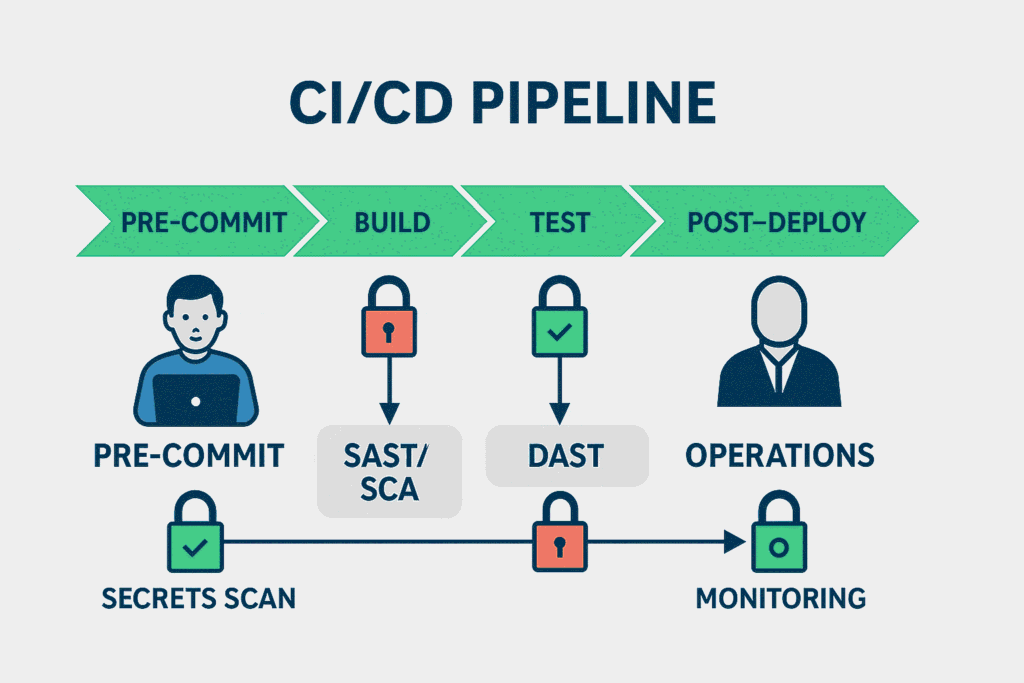
A Secure SDLC becomes scalable only through automation. Add Automated Security Gates:
| CI/CD Stage | Security Control |
|---|---|
| Pre-commit | Secrets scanning |
| Build | SAST, SCA |
| Test | DAST, dependency checks |
| Deploy | IaC scan, container scan |
| Post-deploy | Runtime monitoring |
Recommended Tools:
- GitHub Advanced Security
- GitLab Secure
- Snyk
- Semgrep CI
- OWASP ZAP
- Trivy
- HashiCorp Vault
- Aqua CSPM or Wiz
Automation removes guesswork and ensures consistency.
Step 5: Build a Software Security Champion Program
This is the “secret weapon” behind world-class SDLCs. Security Champions:
- Embed security in every squad
- Become local experts
- Triage vulnerabilities faster
- Reduce dependency on the AppSec team
- Improve cross-functional collaboration
Champion Incentives:
- Early access to learning
- Badges, certifications
- Swag (stickers, hoodies)
- Spotlight in engineering all-hands meetings
A strong champion network makes your SDLC resilient.
Step 6: Make Security Measurable (Metrics That Matter)
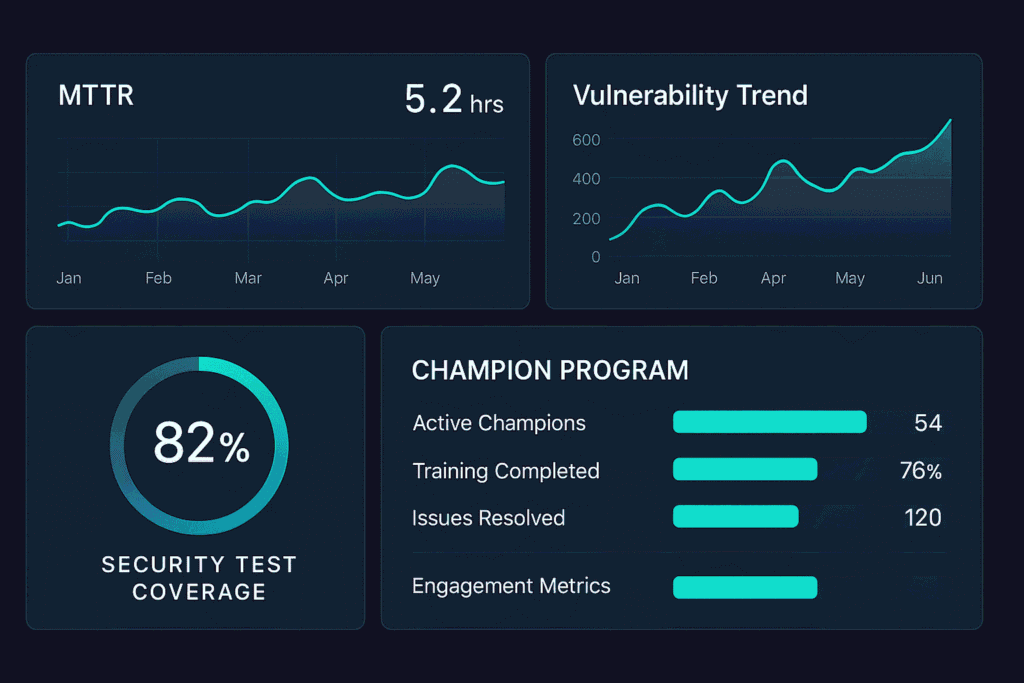
To improve a Secure SDLC, you must measure the health of the program.
Recommended Metrics:
- Mean Time to Remediate (MTTR)
- Vulnerability backlog trend
- Percentage of builds passing security gates
- Coverage of SAST/SCA/DAST
- Champion program engagement
- Percentage of apps threat modelled
- Percentage of code using approved libraries
Avoid vanity metrics: (Number of vulnerabilities found does not equal success). Focus on metrics that reflect risk reduction.
Step 7: Build Security Culture (The Hard Part)
Culture determines whether your Secure SDLC survives long term.
Actions that strengthen culture:
- Give developers autonomy
- Run monthly security clinics
- Publish internal security newsletters
- Conduct hackathons / CTFs
- Celebrate developers who fix vulnerabilities fastest
- Document everything transparently
Avoid a Culture of Fear: Don’t shame developers for introducing vulnerabilities – help them prevent them.
Comparison: Traditional SDLC vs Secure SDLC
| Traditional SDLC | Secure SDLC |
|---|---|
| Security at end | Security from start |
| Manual reviews | Automated CI/CD gates |
| No threat modelling | Threat modelling integrated |
| Security team owns everything | Developers + champions |
| Reactive | Proactive |
| High cost to fix issues | Low cost to fix early |
A secure SDLC is not more work – it is smarter work.
Key Insights & Common Mistakes to Avoid
- Mistake #1: Buying tools before fixing processes. Always build the process then select tools.
- Mistake #2: Overloading developers. Security should simplify engineering, not slow them down.
- Mistake #3: Too many policies, not enough automation. Policies without automation become wishful thinking.
- Mistake #4: No prioritization. Not all vulnerabilities matter. Risk-based prioritization is essential.
- Mistake #5: Attempting everything at once. Start small, scale fast.
Conclusion: Your Secure SDLC Blueprint Starts Today
Building a Secure SDLC from scratch may look intimidating, but it’s absolutely achievable with the right approach.
Start with:
- Vision & governance
- Baseline assessment
- Core controls for each SDLC phase
- Automation in CI/CD
- Champion network
- Measurable metrics
- Security culture
Every organization’s journey will look different, but the principles remain universal: shift left, automate more, reduce friction, empower developers, and protect the business.
For more information on security frameworks, refer to the OWASP SAMM framework and NIST SSDF guidelines.




