Introduction: The Relentless Race and the North Star
The digital landscape is a constantly evolving battleground. For every innovative stride forward from microservices to serverless there’s a new, subtle vulnerability waiting to be exploited. In this relentless race, the OWASP Top 10 stands as a critical beacon, guiding engineers through the tumultuous waters of web application security.
The original OWASP Top 10 was groundbreaking in its simplicity and impact, democratizing critical security knowledge. Yet, despite its visibility, the same fundamental security mistakes persist. As we look toward the 2025 update, it’s not just about knowing the list it’s about understanding why this iteration matters more than ever before for building truly resilient systems.
In my work leading AppSec programs and coaching engineering teams, I’ve seen one truth that transcends tools, tech stacks, and timelines: Security isn’t about finding vulnerabilities. It’s about avoiding the same ones over and over again.
This guide breaks down why the OWASP Top 10 (2025) should be your north star, what’s changed in the risk landscape, and how to practically use it to build software that is secure by design, not secure by accident.

The Ever-Shifting Sands: Core Themes of OWASP Top 10 (2025)
The OWASP Top 10 isn’t a static document; it’s a living guide updated periodically to reflect the current realities of cyber warfare. The 2025 update is poised to address a significant paradigm shift in how we build, deploy, and secure applications.
Moving Beyond Bugs to Design Flaws
The most crucial shift in the modern OWASP Top 10 iterations, particularly 2021 and the anticipated 2025 update, is the move from simple, exploit-based bugs (like basic SQL Injection) to systemic architectural security failures.
| 2025 Core Themes | Implication for Engineers |
|---|---|
| A04: Insecure Design (Elevated Importance) | Security must be integrated during Threat Modeling and architecture reviews, not just coded later |
| Increased API Security Focus | Requires granular validation and authorization checks, specifically targeting BOLA (Broken Object Level Authorization) |
| Supply Chain Risks | Mandatory use of SBOMs (Software Bill of Materials) and continuous integrity verification for all dependencies |
| Cloud-Native Misconfigurations | Focus on insecure defaults in IaaS/PaaS, overly permissive IAM roles, and serverless function exposure |
This isn’t just an update—it’s a recalibration emphasizing Shift Left—embedding security controls at the earliest design phases.
Practical Deep Dive: Why These Categories Dominate Breaches
For engineers, understanding why a category makes the list is more important than memorizing its number. These categories dominate breaches because they are subtle, pervasive, and often missed by automated tools.
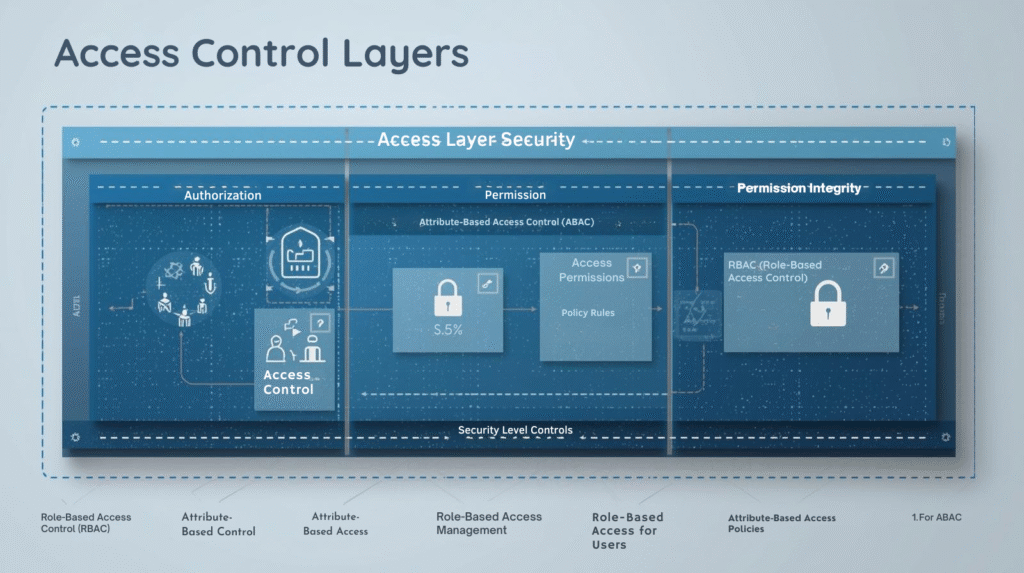
1. Broken Access Control (A01) — The Hydra of Authorization
Why it matters more than ever:
The microservices and API boom means authorization logic is no longer centralized. It is distributed across dozens of endpoints, functions, and roles. This complexity is where failures occur.
Engineer’s Mindset:
Assume every incoming request is hostile, even if the user is authenticated. You must validate who is making the request, what resource they are requesting, and whether they are authorized to access that specific instance of the resource.
Key Defense:
Implement Attribute-Based Access Control (ABAC) or Role-Based Access Control (RBAC) consistently across all data access layers.
2. Insecure Design (A04) — The Unpatchable Flaw
Why it matters more than ever:
Most major, catastrophic breaches are due to flaws in design, not code. Examples include failing to segment high-risk data, trusting client-side authorization, or allowing overly permissive internal network access.
Engineer’s Mindset:
A security bug can be patched. A security design flaw requires re-engineering. If you skip threat modeling—even a simple STRIDE analysis—you are accepting design debt that will cost 10× more to fix later.
Practical Defense:
- Conduct mandatory, documented threat modeling before coding new features
- Enforce secure design principles like defense-in-depth and least privilege at the architecture level
3. Software and Data Integrity Failures (A08) — The Supply Chain Threat
Why it matters more than ever:
The widespread use of third-party, open-source dependencies (NPM, PyPI, Maven) has turned the software supply chain into a critical attack vector. The 2025 list reinforces that compromising a build pipeline or a package registry (like SolarWinds and Log4j) is more efficient for attackers than compromising a single application.
Engineer’s Mindset:
You are only as secure as your weakest dependency. Trust nothing that hasn’t been verified.

Practical Defense:
- Generate and maintain SBOMs to list all dependencies using tools like OWASP Dependency-Track
- Implement continuous SCA (Software Composition Analysis) scanning
- Use signed packages and verify code integrity throughout the CI/CD pipeline
Integrating OWASP Top 10 into the Modern SDLC (DevSecOps)
The OWASP Top 10 should not be a checklist used at the end; it must be a language that guides engineering decisions across the entire Software Development Life Cycle (SDLC).
Actionable Tips for Engineers to Start Today
Adopt a “Top 3 per Sprint” Mindset
Focus security efforts on the categories that cover the most risk:
- A01 (Access Control)
- A03 (Injection)
- A05 (Configuration)
Build a Reusable Secure Pattern Library
Don’t reinvent security. Create internal libraries for common components like:
- Hardened authentication and token validation functions
- Centralized, context-aware input encoding utilities
- Secure database access layers (using prepared statements by default)
Use OWASP Cheat Sheets as PR Templates
Embed links to relevant OWASP Cheat Sheets directly into your Pull Request (PR) templates. This forces developers to perform a quick, self-directed security review before merging.
Automate Everything Feasible
Automation removes human inconsistency and scales security across large codebases:
- SAST: Catch A03, A06 early using tools like SonarQube
- DAST: Test A01, A07 on running applications
- IaC Scanning: Catch A05 in Terraform/CloudFormation using Checkov or Terrascan
OWASP Top 10 Implementation Checklist
| Phase | Activities | Tools & Resources |
|---|---|---|
| Design | Threat modeling, Security requirements | OWASP ASVS, MITRE ATT&CK |
| Development | Secure coding, Peer review | SAST Tools, Secure Code Training |
| Testing | Security testing, Penetration testing | OWASP ZAP, Burp Suite |
| Deployment | Infrastructure security, Runtime protection | CIS Benchmarks, Container Security |
Conclusion: Security Isn’t Optional — It’s Engineering Maturity
The OWASP Top 10 (2025) is a mirror. It reflects what the engineering world keeps getting wrong as we move deeper into cloud-native, API-driven architectures.
For engineers, this shift demands continuous learning and a fundamental change in mindset: moving from reactive patching to proactive, security-by-design thinking. It’s about designing systems to be inherently resilient to attack, not just adding security as a bolted-on feature.
As long as attackers keep exploiting the same weaknesses, OWASP will remain the most important guide for building resilient, trustworthy systems.
The biggest win you can give your product—and your users—is simple:
Bake the OWASP Top 10 into how your team thinks, not just how your app is scanned.
Use it to guide your design, your development patterns, and your overall engineering maturity.



