1. Introduction: The Identity-Centric Battlefield
In the modern cybersecurity paradigm, the perimeter has effectively dissolved. The traditional “castle and moat” architecture, which relied on hardened network boundaries to protect soft internal assets, has been rendered obsolete by cloud integration, remote workforces, and the ubiquity of mobile devices. In this new reality, identity has become the new perimeter, and Microsoft Active Directory (AD) serves as the central nervous system of this identity infrastructure for the vast majority of Global 500 enterprises. Consequently, the “diagram” of an attack path referenced in security discussions almost invariably depicts a trajectory from a low-privileged foothold to the compromise of the Domain Controller (DC) the repository of all trust and authority within a Windows environment.compromise of the Domain Controller (DC) the repository of all trust and authority within a Windows environment. Understanding these Active Directory attack paths is critical for modern cybersecurity defense.
To understand the scale of this threat, recent analysis shows that Active Directory attacks have surged by 42%, making comprehensive knowledge essential for defenders.
The path to the Domain Controller is rarely a direct line. It is a complex graph of relationships, a chain of misconfigurations, and an abuse of legitimate protocols. Attackers do not merely “break” Active Directory; they leverage its own features—Delegation, Replication, Automation, and Trust—against it. From the initial phishing email to the forging of a Golden Ticket, the adversary operates by navigating the identity infrastructure, exploiting the disconnect between the intended architectural design and the operational reality of legacy environments. This report provides an exhaustive, technical analysis of the mechanisms adversaries employ to traverse this path. It dissects the kill chain from initial reconnaissance to total domain dominance, detailing specific techniques such as Kerberoasting, NTLM relaying, ACL abuse, and the exploitation of Active Directory Certificate Services (AD CS). By synthesizing technical mechanics with strategic insights, this analysis elucidates not just what attackers do, but why these vulnerabilities persist and how they are chained together to achieve the “Holy Grail” of cyber espionage: Domain Admin privileges.
The concept of the “attack path” is central to understanding modern adversarial tradecraft. It represents a sequence of abusable relationships (edges) between objects (nodes) that allows an attacker to transitively gain control over the target. This report will systematically dismantle the components of these paths, examining the reconnaissance techniques that reveal them, the credential theft methods that facilitate traversal, and the advanced exploitation vectors that bypass traditional defenses.
Active Directory Attack Paths – Interactive Threat Lab
This interactive lab visually demonstrates how attackers move through Active Directory attack paths, from initial compromise to full Domain Controller dominance, using real-world techniques and scenarios.
Explore Active Directory Attack Paths →2. Phase I: The Initial Foothold and Silent Reconnaissance
Before an adversary can threaten the Domain Controller, they must establish a presence within the environment and construct a mental or digital map of the terrain. The initial phase of an AD compromise is characterized by a shift from external penetration to internal navigation. Unlike traditional exploits that rely on software vulnerabilities, modern AD attacks often “live off the land,” utilizing legitimate administrative tools and native protocols to map the environment without triggering malware signatures.
2.1 The Entry Vector: From Outsider to Insider
The trajectory toward the DC rarely begins with a zero-day exploit against the DC itself. Instead, it commences at the workstation level, typically through the compromise of a standard user’s endpoint. Research indicates that phishing remains a primary entry vector, where adversaries compromise a standard user’s endpoint to gain access to the domain context. Once inside, the attacker possesses a valid domain account—albeit one with low privileges—which is sufficient to query the directory and begin the enumeration phase.
In scenarios where credential harvesting via phishing is unsuccessful, attackers may employ network-level poisoning to capture authentication hashes. In many environments, when a system fails to resolve a hostname via DNS, it falls back to legacy protocols like Link-Local Multicast Name Resolution (LLMNR) or NetBIOS Name Service (NBT-NS). Attackers utilize tools such as Responder to listen for these broadcasts. By spoofing a response, the attacker tricks the victim machine into sending its credentials (in the form of an NTLMv2 hash) to the attacker. These hashes can then be cracked offline or relayed to other systems to gain access. This effectively grants the attacker their initial foothold: a valid set of credentials for a domain user. This is one of the Top 10 Active Directory Attack Methods that defenders must guard against.
2.2 Graph Theory and the BloodHound Revolution
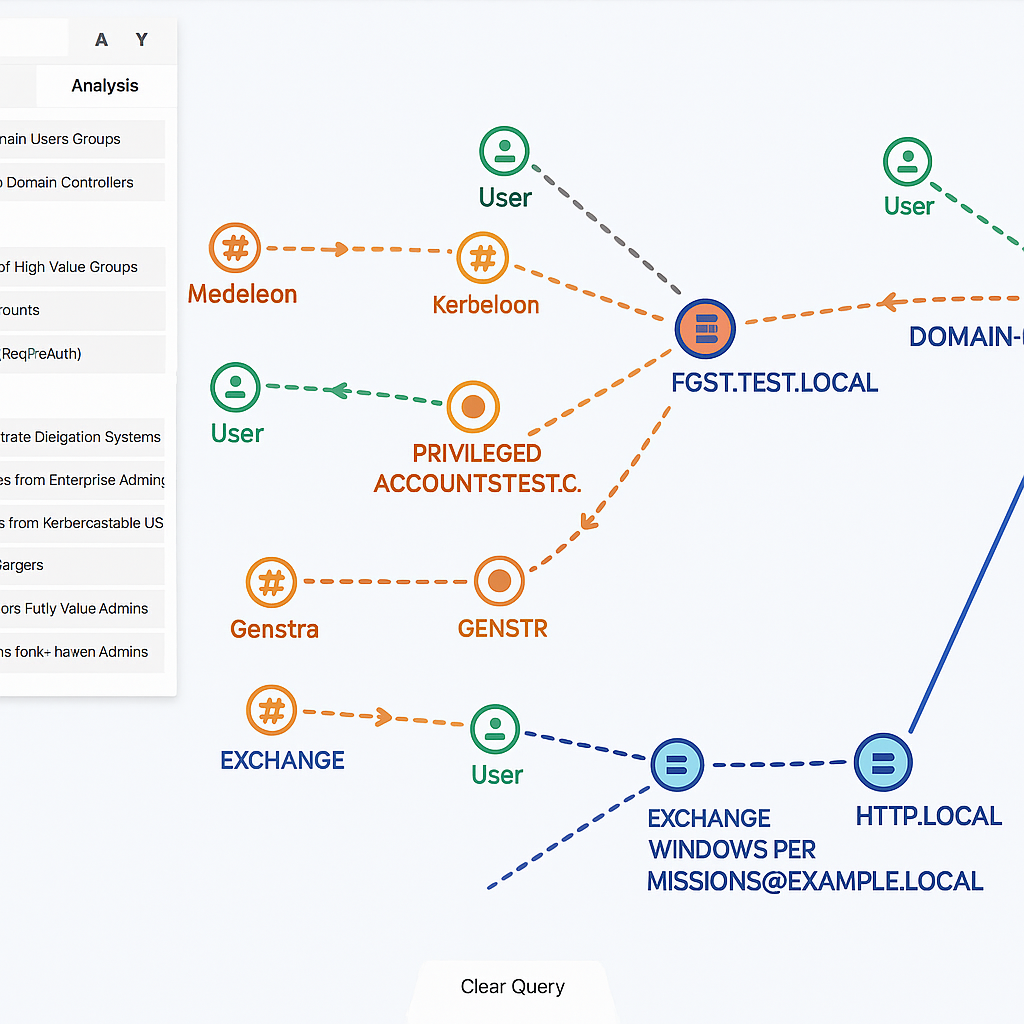
Once a foothold is established, the attacker’s immediate goal is to map the “shortest path” to the Domain Admin group or the Domain Controller. This necessity has driven the adoption of Graph Theory in offensive operations, revolutionized by tools like BloodHound. BloodHound visualizes AD relationships by mapping entities (Users, Groups, Computers) as Nodes and permissions (MemberOf, GenericAll, WriteDACL) as Edges.
The operational value of BloodHound lies in its ability to reveal non-obvious relationships. A standard user might not have direct access to the DC, but they might have ForceChangePassword rights over a user who is a local administrator on a server where a Domain Admin has an active session. BloodHound automates the discovery of these transitive paths, transforming lateral movement from a stochastic guessing game into a calculated traversal of the graph.
| Concept | Description in AD Context | Tactical Value to Attacker |
|---|---|---|
| Node | An object within the directory: User, Computer, Group, GPO, or Domain. | Identifies high-value targets (e.g., Domain Admins, Backup Servers) and potential pivot points. |
| Edge | The relationship between nodes: MemberOf, AdminTo, HasSession, GenericAll, WriteDACL. | Identifies the specific “step” or action an attacker can take to move from one node to another. |
| Path | A sequence of edges connecting a starting node (compromised user) to a destination node (DC). | Reveals hidden, multi-hop escalation routes (e.g., User A -> Group B -> Local Admin on Machine C -> Session of Admin D -> Domain Admin). |
One of the most critical insights BloodHound provides is the HasSession edge. This indicates that a specific user is currently logged onto a specific computer. If an attacker can compromise a computer where a Domain Admin has an active session, they can harvest that administrator’s credentials from memory (LSASS). This “derivative admin” concept is fundamental to modern lateral movement strategies, as it directs the attacker not to the target itself, but to the location where the target’s credentials currently reside. For a deep dive into using this tool from both offensive and defensive perspectives, see this expert guide on mastering BloodHound.
2.3 Native Protocol Enumeration: LDAP and SPNs
While tools like BloodHound are powerful, sophisticated attackers frequently bypass custom tools in favor of native protocols to evade detection by Endpoint Detection and Response (EDR) systems. The Lightweight Directory Access Protocol (LDAP) serves as the primary mechanism for this reconnaissance.
Using standard LDAP queries, attackers download the entire directory structure. This enumeration targets specific attributes that reveal the security posture of the domain:
- User Descriptions: Attackers scan the description attribute of user objects, looking for passwords or notes left by administrators (e.g., “Service Account for Backup, pwd: Password123”).
- Group Memberships: Enumerating the memberOf attribute allows attackers to map the hierarchy of privilege, identifying which users belong to high-value groups like “Domain Admins,” “Enterprise Admins,” or “Backup Operators”.
- Service Principal Names (SPNs): Attackers scan for accounts associated with services by querying for the presence of the servicePrincipalName attribute. This is a critical precursor to Kerberoasting (discussed in Phase II) and is indistinguishable from legitimate service ticket requests in many logs.
- Pre-Authentication Status: Attackers query for the userAccountControl attribute to identify accounts where Kerberos Pre-Authentication is disabled, setting the stage for AS-REP Roasting.
This “silent reconnaissance” allows the attacker to build a target list without executing a single exploit code or dropping a malicious binary. They simply ask the Domain Controller for information it is designed to provide to any authenticated user. Research by Horizon3.ai details how this “Quiet Attack Path” can lead to domain compromise in minutes.
3. Phase II: Credential Access and Identity Theft
With a map of the network and a target list in hand, the adversary moves to upgrade their privileges. The transition from a “Standard User” to a “Privileged User” often relies on abusing the Kerberos authentication protocol. These attacks are particularly dangerous because they exploit the architecture of the protocol itself—specifically its reliance on tickets and shared secrets—rather than a vulnerability in the software code.
3.1 Kerberoasting: Exploiting Service Account Architecture
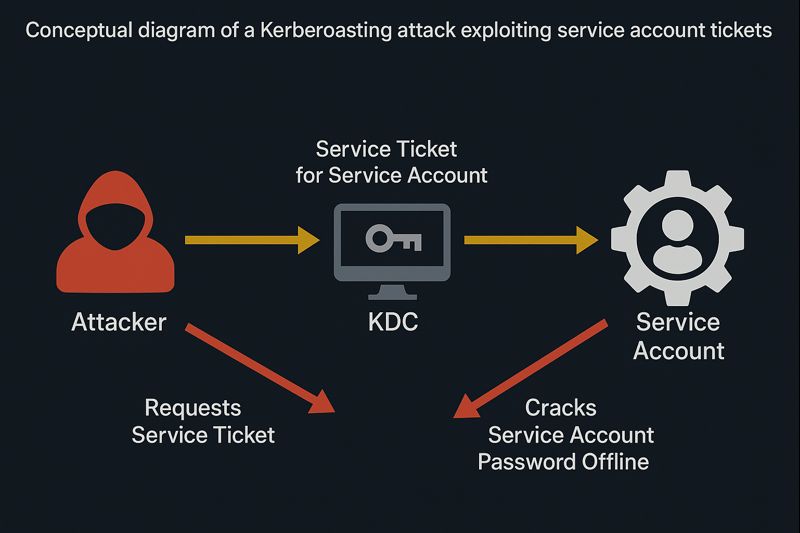
Kerberoasting is a ubiquitous technique in AD attack paths because it can be executed by any authenticated user and requires no special privileges. It specifically targets service accounts, which are often configured with weak passwords yet possess elevated privileges. You can learn more about how to keep your Active Directory safe from Kerberoasting.
The Mechanics of the Attack:
- SPN Identification: The attacker identifies user accounts that have a Service Principal Name (SPN) set. These are typically service accounts (e.g., SQL Service, IIS) used to run applications.
- TGS Request (TGS-REQ): The attacker requests a Kerberos Ticket Granting Service (TGS) ticket for the target service from the Domain Controller. The DC, adhering to the Kerberos protocol, issues the ticket. Crucially, a portion of this ticket is encrypted with the NTLM hash of the service account’s password.
- Hash Extraction and Cracking: The attacker extracts this encrypted ticket from memory. The cracking process happens offline, away from the defender’s sensors. The attacker uses tools like Hashcat to brute-force the password hash. If the service account has a weak password, the attacker recovers the plaintext credentials.
Strategic Implication: Service accounts often possess excessive privileges (e.g., Local Admin on servers, or even Domain Admin rights) and are rarely rotated due to fear of breaking legacy applications. This makes them a high-yield target. The detection of this attack relies on monitoring for Event ID 4769 (A Kerberos service ticket was requested), specifically looking for unusual volumes of requests or requests for RC4 encryption (Ticket Encryption Type 0x17), which is easier to crack than AES.
3.2 AS-REP Roasting: Targeting Pre-Authentication
While Kerberoasting targets service tickets (TGS), AS-REP Roasting targets the initial authentication step (AS-REQ). By default, Kerberos requires “Pre-Authentication,” where the user encrypts a timestamp with their password hash to prove their identity before the DC issues a ticket. However, some accounts have the Do not require Kerberos preauthentication flag enabled in their userAccountControl attribute.
The Attack Vector:
An attacker sends an AS-REQ (Authentication Service Request) for a user with Pre-Auth disabled. The DC responds with an AS-REP (Authentication Service Reply) which contains a chunk of data encrypted with the user’s password hash. The attacker captures this reply and attempts to crack it offline. This technique is stealthier than Kerberoasting as it involves interaction with the authentication service rather than the ticket-granting service, and requires no prior knowledge of the user’s password, only their username.
3.3 Password Spraying
Brute-force attacks, which try many passwords against one account, are noisy and lead to account lockouts. To avoid this, attackers employ “Password Spraying,” where they try a single common password (e.g., “Winter2024!”) against all users in the domain. This low-and-slow approach avoids triggering lockout policies while statistically guaranteeing success in large organizations where at least one user is likely to have a weak password. This method is consistently listed among common Active Directory attack methods.
3.4 Pass-the-Hash (PtH) and Pass-the-Ticket (PtT)
When plaintext passwords cannot be recovered, attackers use the cryptographic proofs themselves. The Windows authentication architecture allows for the reuse of these proofs, decoupling authentication from the knowledge of the plaintext password.
- Pass-the-Hash (PtH): In Windows environments using NTLM, the password hash (NTLMv2) is mathematically sufficient to authenticate to other systems. Tools like Mimikatz allow an attacker to inject a stolen NTLM hash into a new session, effectively “becoming” the user. This is particularly effective for lateral movement to systems where the compromised user has local administrative rights.
- Pass-the-Ticket (PtT): In Kerberos environments, the “Ticket” (TGT or TGS) is the proof of identity. If an attacker compromises a machine, they can extract cached Kerberos tickets from the lsass.exe process and inject them into their current session. This allows them to access network resources as the victim user until the ticket expires, bypassing the need for the password or hash entirely.
4. Phase III: The Mechanics of Lateral Movement
Lateral movement is the act of pivoting from the initial foothold to other systems in the network, specifically hunting for the Domain Controller or the credentials that unlock it. As security controls have evolved, so too have the mechanisms for this movement, shifting from file-based execution to “Living off the Land” (LotL) techniques. For a broader understanding of how these threats connect, consider the expanding cybersecurity threat landscape of 2025.
4.1 Windows Management Instrumentation (WMI): The Stealthy Pivot
WMI is a potent infrastructure management framework that has become a staple of modern lateral movement. It allows for remote process creation, data query, and system configuration. Unlike PSEXEC, which creates a visible service, WMI interactions can be blended with legitimate administrative traffic.
Technical Mechanics:
Attackers typically use the Win32_Process class to invoke the Create method on a remote host. This spawns a new process (e.g., PowerShell or cmd.exe) on the target machine. More sophisticated attackers utilize the MSFT_MTProcess class (available on Windows Server 2016+) or the CIM_LogicFile class to evade detections specifically tuned for Win32_Process abuse.
Stealth Factors: WMI traffic runs over DCOM/RPC, which is common in enterprise networks. By using WMI, the attacker avoids dropping files to disk, executing their payload directly in memory or via standard system binaries, complicating forensic analysis.
4.2 Windows Remote Management (WinRM)
WinRM is the implementation of the WS-Management protocol, used by PowerShell Remoting. It is the modern, firewall-friendly alternative to DCOM/RPC, operating over ports 5985 (HTTP) and 5986 (HTTPS).
WinRM Plugins and Persistence:
Advanced adversaries can abuse the WinRM architecture by registering malicious plugins. A WinRM plugin is a DLL loaded by the WinRM service (wsmprovhost.exe) to handle specific requests. By modifying the registry to register a malicious DLL as a plugin, an attacker can achieve persistence or execute code every time the WinRM service handles a request. This technique is highly stealthy as the code executes within the context of the trusted WinRM service process.
Detection: Detection requires monitoring for unusual parent-child process relationships, such as wsmprovhost.exe spawning unexpected binaries like cmd.exe or powershell.exe, and inspecting registry changes associated with WinRM plugin registration.
4.3 SMB and RPC Beaconing
Traditional lateral movement often utilizes Server Message Block (SMB) named pipes. Tools like PsExec (or Cobalt Strike’s implementation of it) use SMB to upload a service binary to the administrative ADMIN$ share of a target and execute it. While effective, this method is “noisy” due to the file drop and service creation events (Event ID 7045), making it easily flagged by modern AV. Consequently, attackers prefer RPC (Remote Procedure Call) or WMI methods that do not involve file drops.
5. Phase IV: The Silent Escalation via Access Control Lists (ACLs)
A nuanced understanding of Active Directory reveals that “Domain Admin” is not the only path to the DC. Access Control Lists (ACLs) on AD objects often contain misconfigurations that allow for indirect takeover. Attackers exploit these “toxic” ACLs to gain control over high-value objects without triggering alarms associated with group membership changes. This is a classic example of Broken Access Control, a top critical security risk.

5.1 Critical ACL Primitives
Active Directory objects (Users, Groups, OUs) have Discretionary Access Control Lists (DACLs) defining who can perform what actions on them. BloodHound is instrumental in identifying these combinations. Understanding edges like GenericAll and WriteDACL is key.
- GenericAll (Full Control): This is the most dangerous permission. If an attacker has GenericAll over a target user, they can reset the target’s password, effectively taking over the account. If the target is a group, they can add themselves to it.
- WriteDACL: An attacker with WriteDACL rights can modify the ACL of the target object. They can grant themselves GenericAll, subsequently taking full control.
- WriteOwner: This allows the attacker to change the owner of an object to themselves. As the owner, they implicitly have the right to modify the ACL, allowing them to grant full control permissions.
- ForceChangePassword: This specific extended right allows the principal to reset a user’s password without knowing the current one. If an attacker finds this permission over a Domain Admin account, the path to the DC is complete. Learn more about abusing ACL misconfigurations.
5.2 Exploiting Organizational Units (OUs)
Often overlooked, permissions on OUs are inherited by the objects inside them. If an attacker gains GenericWrite or Manage Group Policy Links permissions on an OU that contains the Domain Controllers, they can execute a devastating attack.
- GPO Linking: The attacker can link a malicious Group Policy Object (GPO) to the compromised OU.
- Execution: When the Domain Controller updates its policy (every 90 minutes or upon reboot), it will execute the settings defined in the malicious GPO (e.g., creating a local admin, running a startup script, or scheduling a task). Since the GPO applies to the Computer object of the DC, this results in SYSTEM-level compromise.
5.3 AdminSDHolder and SDProp Persistence
For long-term persistence, attackers abuse the AdminSDHolder object. Active Directory has a background process called SDProp that runs every 60 minutes. It checks protected groups (like Domain Admins) and resets their ACLs to match the ACL of the AdminSDHolder object to prevent accidental misconfiguration.
- The Attack: An attacker modifies the ACL of the AdminSDHolder object to give a hidden backdoor user “Full Control.”
- The Persistence: Every 60 minutes, AD automatically propagates this permission to every Domain Admin account. Even if defenders manually remove the attacker’s permissions from a Domain Admin, SDProp will re-add them within the hour, ensuring the attacker maintains access.
6. Phase V: Active Directory Certificate Services (AD CS) Exploitation
In recent years, security researchers have highlighted Active Directory Certificate Services (AD CS) as a massive attack surface. AD CS is the “PKI” (Public Key Infrastructure) of the Microsoft world, issuing digital certificates for authentication. Misconfigurations here are catastrophic because a valid certificate allows an attacker to request a Kerberos TGT, effectively bypassing password policies and MFA.
6.1 The ESC1 Attack: Misconfigured Certificate Templates
This attack vector targets certificate templates that are overly permissive.
- Vulnerability: A certificate template is configured to allow “Client Authentication” (meaning it can be used to log in) AND has the CT_FLAG_ENROLLEE_SUPPLIES_SUBJECT flag enabled (allowing the requester to specify the Subject Alternative Name, or SAN).
- Exploitation: A low-privileged attacker requests a certificate using this template. In the request, they specify the SAN as “Administrator” or the name of a Domain Controller.
- Result: The CA issues a valid certificate for the Administrator. The attacker uses this certificate to authenticate via PKINIT (Public Key Cryptography for Initial Authentication) and obtains a TGT for the Domain Admin, bypassing all credential requirements. This is detailed in the explanation of the ESC1 Attack.
6.2 The ESC8 Attack: NTLM Relay to AD CS
This attack abuses the Web Enrollment interface of AD CS.
- Vulnerability: The AD CS Web Enrollment interface (running on IIS) typically supports NTLM authentication and does not enforce Extended Protection for Authentication (EPA) or HTTPS signing.
- Exploitation: An attacker coerces a Domain Controller to authenticate to the attacker’s machine (using coercion methods like PetitPotam). The attacker captures the NTLM authentication traffic and “relays” it to the AD CS Web Enrollment server.
- Result: The AD CS server, believing it is communicating with the DC, issues a certificate for the DC’s machine account. The attacker uses this certificate to impersonate the Domain Controller, allowing them to perform DCSync and dump the domain hashes. Microsoft provides guidance on mitigating these NTLM relay attacks on AD CS.
6.3 Shadow Credentials
This technique abuses the msDS-KeyCredentialLink attribute introduced to support Windows Hello for Business.
- The Attack: If an attacker has GenericWrite permissions on a user or computer object, they can populate this attribute with a public key they control.
- Result: They can then authenticate as that user using PKINIT, obtaining a TGT without ever knowing the user’s password or touching lsass. This is a powerful persistence mechanism that bypasses traditional password resets.
7. Phase VI: Delegation, Coercion, and Logic Vulnerabilities
Attackers frequently exploit the mechanisms that allow servers to act on behalf of users (Delegation) and cryptographic flaws in legacy protocols. Understanding these requires a grasp of secure design principles, as failures here often stem from Insecure Design.
7.1 Unconstrained Delegation
Unconstrained Delegation is a legacy setting that allows a server to impersonate a user to any service in the domain.
- The Mechanism: When a user connects to a server with Unconstrained Delegation enabled, the user’s TGT is sent to that server and stored in memory.
- The Attack (“The Printer Bug”): An attacker compromises a server with Unconstrained Delegation (often a backup or SQL server). They then use the “Printer Bug” (MS-RPRN) to force the Domain Controller to connect to this compromised server.
- Result: The DC sends its machine account TGT to the compromised server. The attacker extracts this TGT from memory and uses it to impersonate the DC, leading to immediate domain dominance. You can read a full definition and mitigation guide for unconstrained delegation attacks.
7.2 ZeroLogon (CVE-2020-1472)
ZeroLogon targets the Netlogon Remote Protocol. Due to a cryptographic flaw in the usage of AES-CFB8 (where the initialization vector was set to all zeros), an attacker with network access to the DC can attempt to authenticate by sending a stream of zeros.
- The Impact: Statistically, this authentication attempt will succeed (1 in 256 attempts). Once authenticated, the attacker can send a Netlogon message to set the DC’s computer password to an empty string.
- Dominance: With the DC password known (empty), the attacker can use DCSync to dump all hashes in the domain.
7.3 PrintNightmare (CVE-2021-34527)
This vulnerability in the Windows Print Spooler service allows for Remote Code Execution (RCE).
- The Attack: An authenticated user can remotely install a printer driver on the DC. By specifying a malicious DLL as the driver, the Spooler service (running as SYSTEM) loads and executes the attacker’s code.
- Result: Instant SYSTEM-level access to the Domain Controller.
8. Phase VII: Domain Dominance and Persistence
Once the attacker has administrative access to the Domain Controller, they execute “Domain Dominance” techniques to extract the “crown jewels” and establish persistence that survives password resets. Tools like NetExec can be used in these later stages of an attack simulation.
8.1 DCSync: The Ultimate Extraction
DCSync is not an exploit; it is a feature. It simulates the replication process between Domain Controllers.
- The Action: An attacker with DS-Replication-Get-Changes-All rights (e.g., Domain Admin) requests the password data for specific users (like the KRBTGT account or the CEO) from the DC.
- Stealth: This occurs over the DRSUAPI (replication protocol) and does not involve accessing the NTDS.dit file on disk, making it harder to detect without network monitoring.
8.2 Golden Ticket Attack
With the hash of the KRBTGT (Key Distribution Center Service Account) obtained via DCSync, the attacker holds the keys to the kingdom.
- Forgery: The attacker can forge a TGT for any user, with any privileges, valid for any duration (e.g., 10 years). This is known as a Golden Ticket.
- Power: Even if the attacker loses their compromised accounts, as long as the KRBTGT password isn’t changed (which happens rarely), they can generate new tickets at will to re-enter the network.
8.3 DCShadow
DCShadow takes DCSync a step further. Instead of just asking for data, the attacker registers a rogue workstation as a Domain Controller in the AD replication topology.
- Mechanism: Using lsadump::dcshadow, the attacker forces the legitimate DCs to replicate changes from the rogue DC. This allows the attacker to push malicious changes (like updating the SIDHistory of a user) directly into the directory without leaving standard modification logs.
8.4 DSRM Persistence
The Directory Services Restore Mode (DSRM) account is a local administrator account on the DC, rarely used and often forgotten.
- The Attack: Attackers can change the registry key DsrmAdminLogonBehavior to 2. This allows the DSRM account to log in via the network even when the DC is running normally (not in restore mode).
- Result: Since DSRM passwords are seldom rotated, this provides a stealthy, long-term backdoor into the DC.
9. Strategic Defense: The Enterprise Access Model
Defending against such a multi-faceted kill chain requires moving beyond the “flat” network model to a Tiered Administration model. A robust defense is part of a mature DevSecOps culture.
9.1 The Tier Model vs. Enterprise Access Model
Microsoft originally proposed the Tier Model (Red Forest) to segregate assets.
- Tier 0: Domain Controllers, PKI, and accounts that manage them (Domain Admins).
- Tier 1: Application Servers and their admins.
- Tier 2: Workstations and Helpdesk.
- Rule: A Tier 0 admin never logs into a Tier 1 or Tier 2 asset. This breaks the “Pass-the-Hash” upward trajectory.
The Enterprise Access Model (EAM):
Modern guidance has evolved into the EAM, which integrates cloud (Azure/Entra ID) and Zero Trust principles. It distinguishes between the Control Plane (Tier 0 + Cloud Identity Providers), the Management Plane, and the Data/Workload Plane. This model emphasizes that compromising an Azure Global Admin is functionally equivalent to compromising an on-premise Domain Admin, requiring unified protection strategies. Microsoft’s official documentation on Securing privileged access with the Enterprise Access Model is the authoritative source.
9.2 Detection and Remediation
Defense requires identifying the subtle signals of these attacks.
| Attack Vector | Key Indicator | Mitigation |
|---|---|---|
| Kerberoasting | High volume of TGS-REQ (Event 4769) with RC4 encryption. | Strong, rotated passwords for Service Accounts; Use AES. |
| AS-REP Roasting | Event 4768 with PreAuthType 0. | Enable Pre-Authentication for all users. |
| DCSync | DS-Replication-Get-Changes privileges used by non-DC IP. | Restrict Replicating Directory Changes permission; Monitor API. |
| Unconstrained Delegation | Spooler service traffic; TGTs in memory. | Disable Unconstrained Delegation; Use RBCD. |
| AD CS (ESC1) | Cert request with SAN different from subject; Client Auth EKU. | Disable “Enrollee Supplies Subject” on templates; Manager Approval. |
| NTLM Relay (ESC8) | NTLM login to CA Web Enrollment. | Enable Extended Protection for Authentication (EPA); Require HTTPS. |
| ZeroLogon | Event ID 4742 (Computer account changed) by anonymous. | Patch (CVE-2020-1472); Enforce Secure RPC. |
| AdminSDHolder | Changes to CN=AdminSDHolder object. | Monitor AdminSDHolder for changes; Remove unauthorized ACEs. |
This analysis confirms that the security of the Domain Controller is inseparable from the hygiene of the entire Active Directory forest. Every service account, every certificate template, and every delegation setting is a potential bridge in the attacker’s path to the crown jewels. Security is no longer about keeping intruders out of the network; it is about keeping them out of the directory.




