If there’s one vulnerability category that refuses to fade, it’s Broken Access Control.
According to the OWASP Top 10 2025, Broken Access Control is once again one of the most recurring and most damaging vulnerabilities found in modern applications.
Why? Because unlike injection or cryptographic failures, access control doesn’t break loudly. It breaks quietly. Subtly. Invisibly. And often, by the time someone notices, the damage has already been done.
What Is Broken Access Control? (Human Explanation)

At its core: Broken Access Control happens when users can access data or perform actions they should NOT be able to access.
This is an authorization failure – not authentication. A user is logged in… but they’re allowed to do things far beyond what their role should permit.
Examples include:
- Reading someone else’s messages
- Accessing another customer’s invoice
- Performing admin-only actions
- Changing another user’s settings
- Viewing data belonging to a different tenant
And because these issues often come from “business logic gaps,” they’re incredibly easy to introduce – and incredibly hard for scanners to detect.
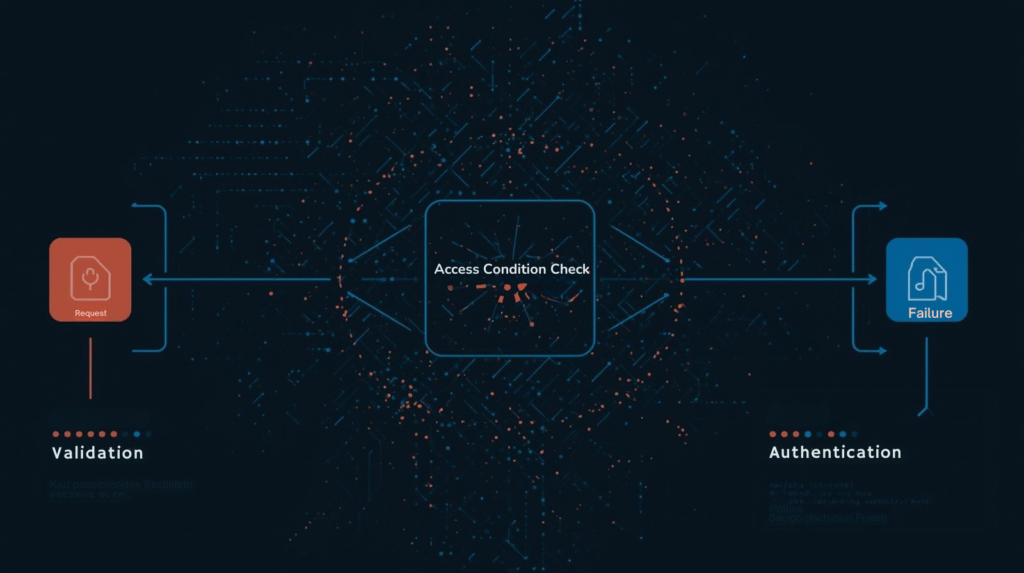
Visual: How Broken Access Control Happens
┌─────────────────┐ ┌─────────────────┐ ┌─────────────────┐
│ User Request │───▶│ Authentication │───▶│ Authorization │───▶│ Action?
└─────────────────┘ └─────────────────┘ └─────────────────┘
│
┌───────▼───────┐
│ Allowed? │
└───────┬───────┘
│
Yes ──────┘ No ──────┐
│ │
▼ ▼
┌─────────────┐ ┌─────────────────┐
│ Action │ │ Access Denied │
│ Allowed │ │ │
└─────────────┘ └─────────────────┘
The system knows who the user is. It just fails to stop them from acting outside their boundaries.
Why It’s Still High in OWASP 2025
The OWASP 2025 data shows:
- It’s one of the most common issues found during assessments
- It’s consistently high impact
- It’s hard to detect automatically
- It’s easy to accidentally introduce during feature development
So even with modern frameworks, improved tooling, and cloud security platforms, Broken Access Control stubbornly remains in the Top 10 – because the problem isn’t technical alone. It’s human and structural.
Common Real World Examples (With Diagrams)
Let’s look at the most common scenarios you’ll encounter with simple diagrams to make them easy to grasp.
1. IDOR (Insecure Direct Object Reference)
Scenario: A user changes an ID in the URL and accesses someone else’s data.
┌─────────────┐ ┌─────────────────────┐ ┌─────────────────────┐
│ Attacker │───▶│ Request: GET /api/ │───▶│ Server Response │
│ │ │ transactions/1002 │ │ │
└─────────────┘ └─────────────────────┘ └──────────┬──────────┘
│
┌───────▼───────┐
│ ❌ FAILED: │
│ No Ownership │
│ Validation │
└───────┬───────┘
│
┌───────▼───────┐
│ Data Leaked │
│ to Wrong │
│ User │
└───────────────┘
If the backend doesn’t verify ownership, the attacker wins.
Why it’s dangerous: It’s simple. It’s quiet. And it often returns full personal or financial data.
2. Missing Function Level Access Control
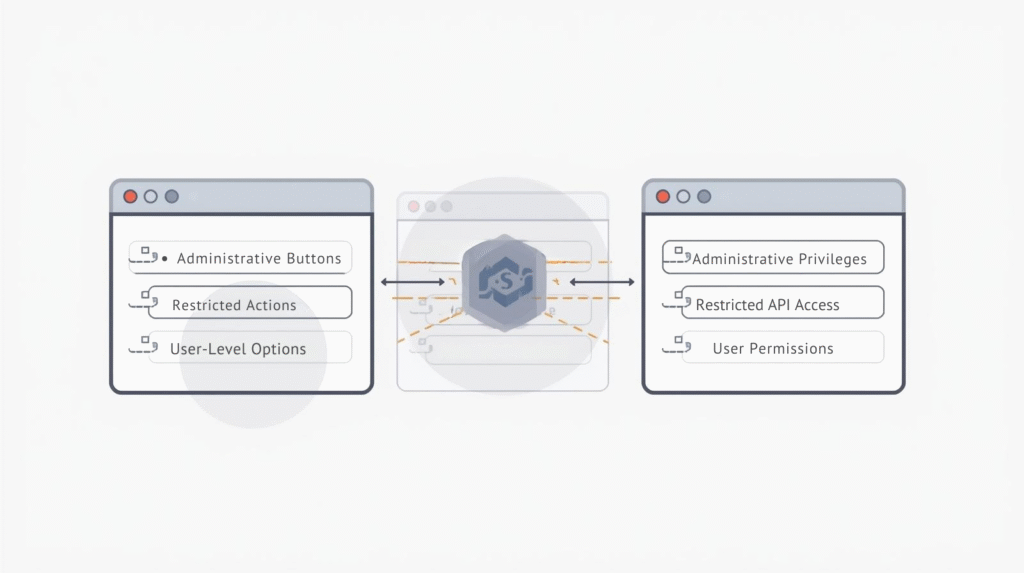
UI hides the admin button. Backend forgets to enforce the rule.
┌─────────────┐ ┌─────────────────────┐ ┌─────────────────────┐
│ Normal │ │ UI Hides Admin │ │ Backend Forgets │
│ User │───▶│ Buttons │───▶│ Authorization │
└─────────────┘ └─────────────────────┘ └──────────┬──────────┘
│
┌───────▼───────┐
│ Admin Action │
│ Executed │
│ Without Auth │
└───────────────┘
Attackers ignore your UI and send raw HTTP requests.
3. Forced Browsing
The classic “direct URL access” bypass.
┌─────────────┐ ┌─────────────────────┐ ┌─────────────────────┐
│ User │───▶│ Access Protected │───▶│ Paywall Blocks │
│ │ │ /premium/ │ │ Directory Access │
└─────────────┘ └─────────────────────┘ └──────────┬──────────┘
│
┌─────────────┐ ┌─────────────────────┐ ┌──────────▼──────────┐
│ Attacker │───▶│ Direct Access to │───▶│ ❌ Files Accessed │
│ │ │ /premium/content1 │ │ Without Payment │
└─────────────┘ └─────────────────────┘ └─────────────────────┘
If deep links aren’t protected, attackers bypass paid features easily.
4. Vertical Privilege Escalation
Normal user becomes admin by simply guessing or accessing an unprotected admin route.
┌─────────────┐ ┌─────────────────────┐ ┌─────────────────────┐
│ Normal │───▶│ Guess/Discover │───▶│ Access Admin │
│ User │ │ Admin Routes │ │ Endpoints │
└─────────────┘ └─────────────────────┘ └──────────┬──────────┘
│
┌───────▼───────┐
│ Privilege │
│ Escalation │
│ Successful │
└───────────────┘
If any of these aren’t protected by server-side checks, it leads to instant privilege escalation.
5. Multi-Tenant Isolation Failures
This one is catastrophic for SaaS companies.
┌─────────────┐ ┌─────────────────────┐ ┌─────────────────────┐
│ Tenant A │───▶│ Request: GET │───▶│ Server Returns │
│ │ │ /tenants/zeon/data │ │ Tenant B's Data │
└─────────────┘ └─────────────────────┘ └──────────┬──────────┘
│
┌───────▼───────┐
│ Cross-Tenant │
│ Data Breach │
│ Occurs │
└───────────────┘
One customer viewing another customer’s data = breach severity zero.
Why Scanners Struggle With This (Even in 2025)
This is where many development teams get blindsided.
Static and dynamic scanners are great at:
- Injection
- XSS
- Outdated libraries
- Misconfigurations
…but they struggle with business logic, because only humans understand:
- “User A should NOT see User B’s invoices.”
- “Only admins should delete accounts.”
- “Tenant isolation must ALWAYS hold.”
Broken Access Control is fundamentally contextual, which is why OWASP repeatedly highlights it as difficult to automate.
Example: How Developers Often Introduce BAC Without Realizing It
Here’s a subtle real-world case:
- The UI hides admin buttons from regular users
- The API endpoint doesn’t validate the user’s role
- A curious tester opens dev tools → Network tab
- They replay the admin API call manually
- It works – because no server-side check exists
This happens a lot in growing applications where new flags or roles get added quickly, but backend authorization isn’t consistently enforced.
How to Prevent Broken Access Control (Practical Steps)
Here are the most effective ways to eliminate (or drastically reduce) Broken Access Control issues.
1. Enforce EVERYTHING on the Server
Never rely on UI controls for protection. If someone sends a request directly via curl or Burp Suite, the server must still verify their permission. No exceptions.
2. Centralize Authorization Checker Logic
Bad pattern:
if (isAdmin)sprinkled everywhere- Logic duplicated in controllers and services
Good pattern:
- Middleware validators
- RBAC/ABAC policy engines
- Centralized “Authorization Service”
- Declarative role-based route protection
If authorization is consistent, errors become harder to introduce.
3. Deny by Default
Security shouldn’t be “open unless restricted.” It should be: Restricted unless explicitly allowed. This one rule prevents entire categories of forced browsing and function-level issues.
4. Test Like a Curious Attacker
Adopt the mindset of a bug bounty hunter:
- Modify IDs
- Access resources not linked in UI
- Call admin endpoints
- Tamper with roles or tokens
- Try tenant hopping
Bug bounty writeups are full of “I just tried changing the ID and it worked” stories – because this approach is incredibly effective.
5. Monitor Suspicious Access Attempts
Detect patterns such as:
- Repeated ID tampering
- Non-admin accounts calling admin APIs
- Attempted access to hidden or unused URLs
- Sequential enumeration of object IDs
Even if a check fails, repeated attempts reveal intent.
Quick Concept Diagram: How Proper Access Control Should Work
┌─────────────────────────────────┐ ┌─────────────────────────────────┐ │ PROPER SYSTEM │ │ BROKEN SYSTEM │ ├─────────────────────────────────┤ ├─────────────────────────────────┤ │ User Request → AuthN → AuthZ │ │ User Request → AuthN → Action │ │ │ │ │ │ │ │ │ │ ▼ ▼ │ │ ▼ ▼ │ │ ┌─────────────┐ ┌─────────────┐ │ │ ┌─────────────┐ ┌─────────────┐ │ │ │ Validate │ │ Check │ │ │ │ Validate │ │ No AuthZ │ │ │ │ Identity │ │ Permissions│ │ │ │ Identity │ │ Check │ │ │ └─────────────┘ └─────────────┘ │ │ └─────────────┘ └─────────────┘ │ │ │ │ │ │ │ │ │ │ └──────┬───────┘ │ │ └──────┬───────┘ │ │ ▼ │ │ ▼ │ │ ┌─────────────┐ │ │ ┌─────────────┐ │ │ │ Action │ │ │ │ Action │ │ │ │ Controlled │ │ │ │ Uncontrolled│ │ │ └─────────────┘ │ │ └─────────────┘ │ └─────────────────────────────────┘ └─────────────────────────────────┘
A LOT of systems authenticate a user… but skip or weaken the authorization stage. That’s where breaches begin.
Access Control Testing Checklist
Authentication Testing
- Test for session management vulnerabilities
- Verify token expiration and validation
- Check for weak password policies
- Test account lockout mechanisms
Authorization Testing
- Test IDOR vulnerabilities across all endpoints
- Verify role-based access controls
- Check privilege escalation possibilities
- Test multi-tenant isolation
Business Logic Testing
- Verify workflow bypass possibilities
- Test for forced browsing vulnerabilities
- Check price manipulation opportunities
- Verify data ownership validation
Additional Resources
OWASP References
Security Standards
Final Thoughts
Broken Access Control is not glamorous. It’s not sensational. It doesn’t make headlines – until it leads to massive data exposure, privilege escalation, or cross-tenant leaks.
That’s why OWASP has kept it firmly in the Top 10 again in 2025.
And the real irony? The vulnerabilities themselves are often shockingly simple – a missing check, a forgotten rule, a misconfigured endpoint. But their consequences? Enormous.
The good news: with strong server-side checks, centralized authorization policy, a deny-by-default mindset, and testing from an attacker’s perspective, you can eliminate most of these issues entirely.
Broken Access Control may be the quietest vulnerability in your stack – but with the right practices, it doesn’t have to be the deadliest.



