A Complete Guide for Security & DevOps Professionals
The Domain Name System (DNS) is one of the most fundamental building blocks of the modern internet yet it’s also one of the most misunderstood areas, even among experienced developers and IT professionals. Whether you’re trying to understand how attackers discover the real server IP behind Cloudflare, setting up a subdomain on a different host, or migrating a website without breaking email services, DNS plays a central role.
In this article, we bring together everything we’ve discussed:
- Why DNS records matter
- How shared hosting works
- How web servers know which domain to serve on a shared IP
- How attackers uncover real server IPs even behind Cloudflare
- The role of TXT records in domain verification
- How to correctly set up subdomains
- How to migrate hosting safely without breaking MX (email) records
Let’s break it all down clearly, simply, and with real-world security context.
1. The Core DNS Records and What They Do
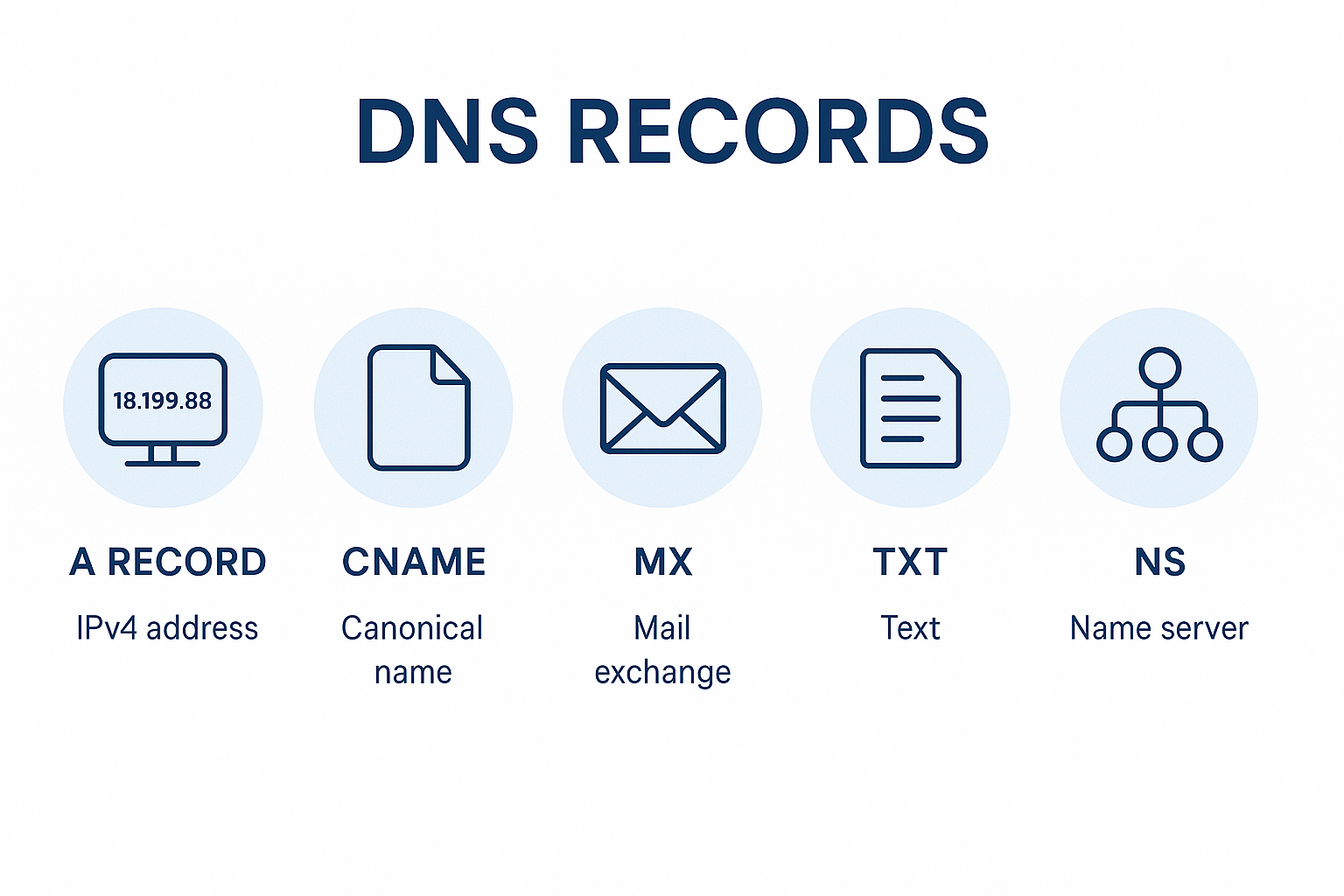
Before diving into advanced scenarios, let’s quickly recap the most important DNS record types and their jobs:
A Record
Maps a domain or subdomain → an IPv4 address.
Example:example.com A 203.1.2.3
CNAME Record
An alias pointing one domain to another.
Example:blog.example.com CNAME myblog.hosting.com
MX Record
Controls where email for your domain is delivered.
Example:example.com MX 10 mail.protonmail.com
NS Record
Points to the authoritative nameservers responsible for your DNS.
Example:example.com NS ns1.synergywholesale.com.au
TXT Record
Stores text data used for:
- Domain verification (Google, Repl.it, AWS, etc.)
- SPF/DKIM/DMARC
- Service configuration
TXT records do not route traffic — they store metadata.
2. Why You Cannot Combine A Records and NS Records
A very common question is:
“Why can’t I mix A and NS records for the same host?”
Answer:
- A Record = where traffic goes
- NS Record = who controls DNS for this domain
These two have completely different jobs. If a domain has an NS record, DNS resolvers must delegate authority to that nameserver. If the same domain also had an A record, this would conflict because the resolver would not know:
- Should it resolve the IP directly (A record)?
- Or should it ask another authority (NS record)?
Therefore:
❌ You cannot set an A record at the exact same label where an NS record delegates authority.
✔ But you can have A records at your root domain even though your root domain has NS records — because those NS records apply at the zone level, not the record level.
3. Why Many Domains Share the Same IP (Shared Hosting)
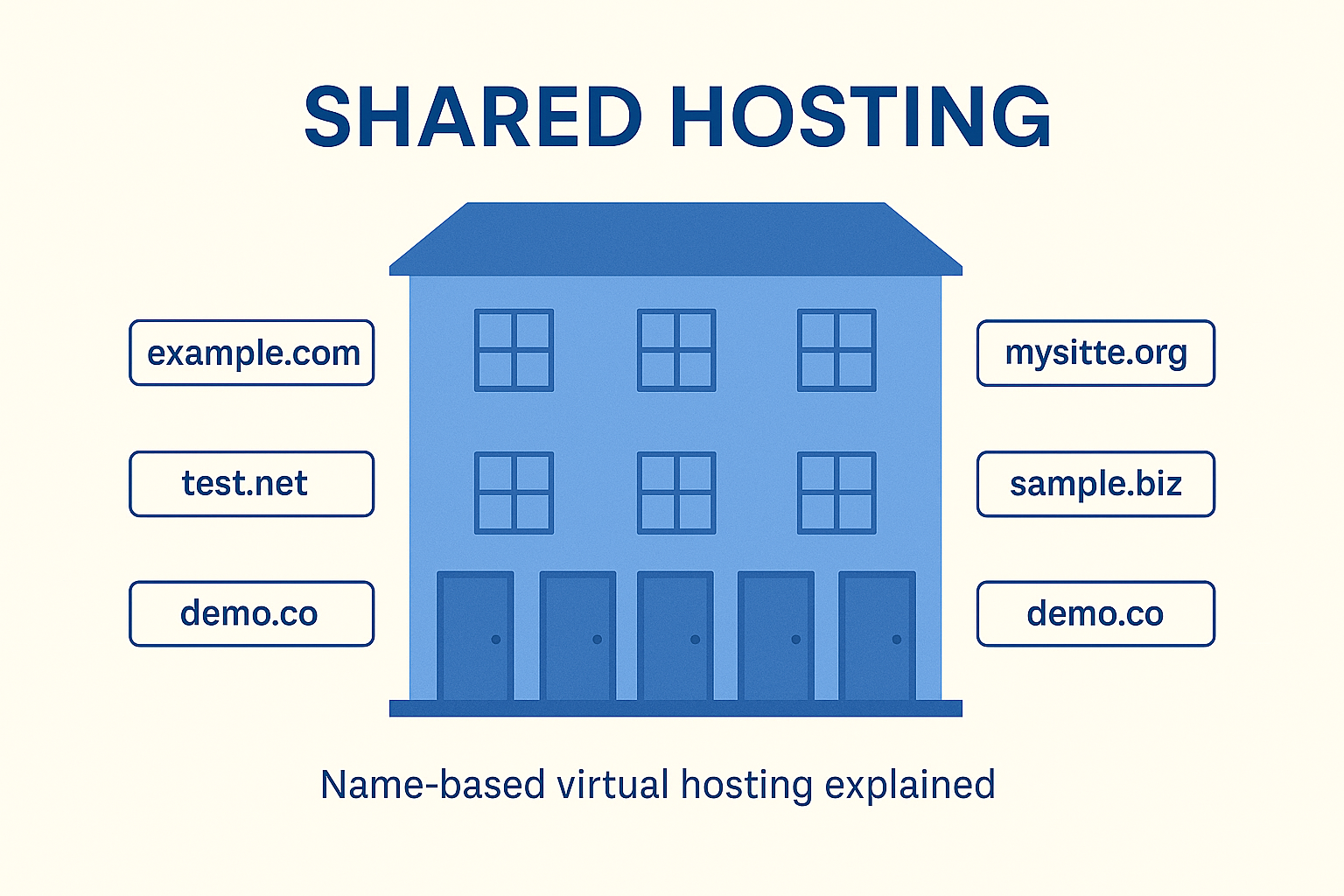
You may have noticed dozens — even hundreds — of unrelated domains pointing to the same server IP. This is perfectly normal. This is called Name-Based Virtual Hosting.
How does the server know which website to show if multiple domains share an IP?
Because every HTTP request contains a Host Header.
Example request:
text
GET / HTTP/1.1 Host: ahsan.au
The web server (e.g., Apache, Nginx, Caddy, IIS) reads the Host header, and based on that value, it selects the correct virtual host configuration. Think of it like an apartment building with one street address (IP), but different unit numbers (domains).
4. How Attackers Discover Real Server IPs (Even Behind Cloudflare/WAF)
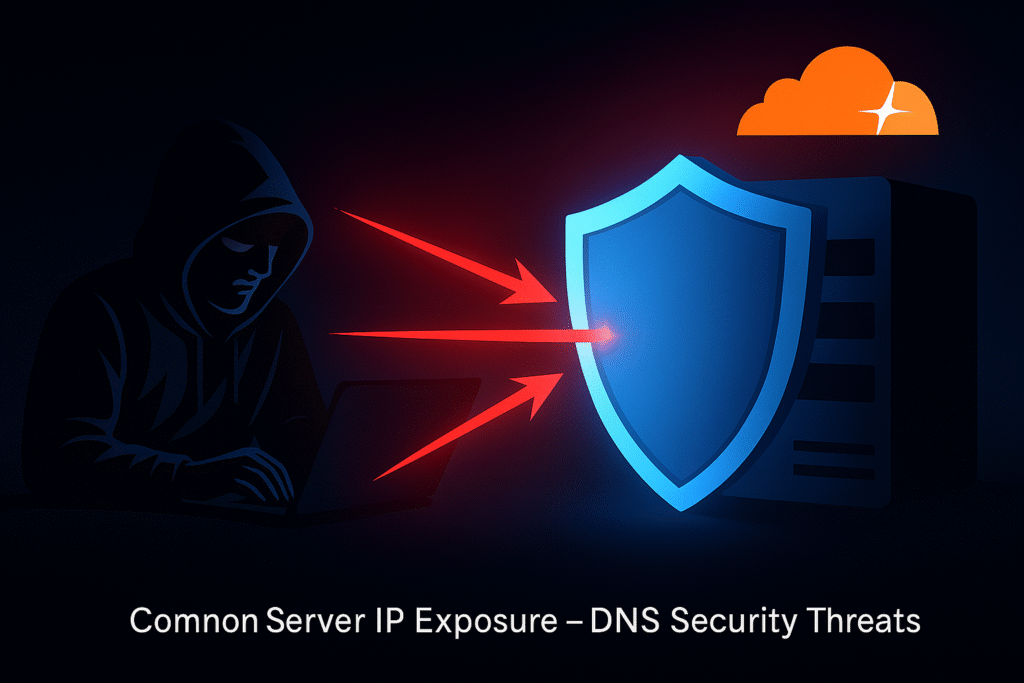
In the real world, most companies protect their origin server IP using:
- Cloudflare
- AWS CloudFront
- Akamai
- Azure Front Door
- Imperva
- Reverse proxies
- WAFs
But attackers can still often uncover the real origin. Here’s how:
A) Historical DNS Lookups
Tools like:
- SecurityTrails
- ViewDNS
- Censys
- Shodan
- PassiveTotal
- DNSDumpster
store historical DNS records. If your site was ever exposed before Cloudflare was added, these sites still have the original IP. You can’t delete this data — it’s archived permanently.
B) Exposed Subdomains
Typical mistake:
www.example.com→ Cloudflare (protected)api.example.com→ direct A record (exposed)dev.example.com→ direct A record (exposed)
One forgotten A record leaks the entire hosting environment.
C) Email Services Leaking Origin
If your mail server and web server are the same machine, an MX lookup may reveal the origin.
Example:example.com MX mail.example.com (203.5.88.19)
Attackers then probe 203.5.88.19 directly.
D) Direct-IP Fingerprinting
If the origin server is misconfigured and responds to direct IP requests, attackers can detect:
- Server banner
- TLS certificate CN/SAN
- Server response patterns
A Cloudflare-protected site accidentally returning your real website on the raw IP is a common misconfiguration.
E) Webhooks or Outbound Calls
If your application makes outbound requests (for example: webhooks, API callbacks, payment gateways):
- The origin IP appears in logs at third-party systems
- Attackers who compromise those systems can learn your origin
This is why webhook.site can be useful in testing — but also dangerous when misconfigured in production systems.
5. How webhook.site Helps in DNS/Web Application Testing
Webhook.site doesn’t receive DNS traffic — it receives HTTP requests. It is useful when:
- You want to see if an external system can make a callback
- You want to inspect headers (e.g., X-Forwarded-For, origin IPs, user-agent)
- You want to test webhook, API notifications, or SSRF pathways
Steps:
- Generate a unique URL on webhook.site
- Configure the app or DNS-triggered event to call that URL
- Trigger the event
- Inspect the incoming request
This is extremely helpful when diagnosing:
- URL callbacks
- OAUTH redirects
- Webhook misconfigurations
- SSRF pathways
- Origin header leakage
6. Understanding TXT Records for Subdomain Verification
TXT records are frequently required in two cases:
(1) Domain Ownership Verification
Services like:
require a TXT record like:_subdomain.example.com TXT "verification=abc123"
This confirms you control the domain.
(2) Email Security
TXT records are used for:
- SPF
- DKIM
- DMARC
These protect against email spoofing.
Important:
TXT records do not point your subdomain anywhere. To route traffic to a server, you must use:
- A record
- or CNAME record
7. Hosting Repl.it on a Subdomain While Main Site Runs on Synergy
Scenario:
- Root domain (
example.au) hosted on Synergy Wholesale - You want
app.example.auto point to Repl.it - Repl.it asks you to add a TXT record
Steps:
- Add TXT record for verification (no routing effect).
- Add either:
- An A record if Repl.it gives you an IP
- Or a CNAME if they give you a hostname
Example:app.example.au A 45.56.88.12
This routes only the subdomain — NO conflict with your main site.
8. Can You Have More Than One CNAME Record?
Short answer:
❌ Not for the same subdomain.
You can only have one CNAME per hostname. But you can have:
- Different A records for different subdomains
- Different CNAME records for different subdomains
Example (valid):
text
example.au A 203.1.2.3 app.example.au A 45.22.33.11 dev.example.au CNAME app.example.au
Example (invalid):
text
app.example.au CNAME repl.it app.example.au CNAME other.host.com <- conflict
9. How to Migrate Hosting Without Breaking Email (MX Records)
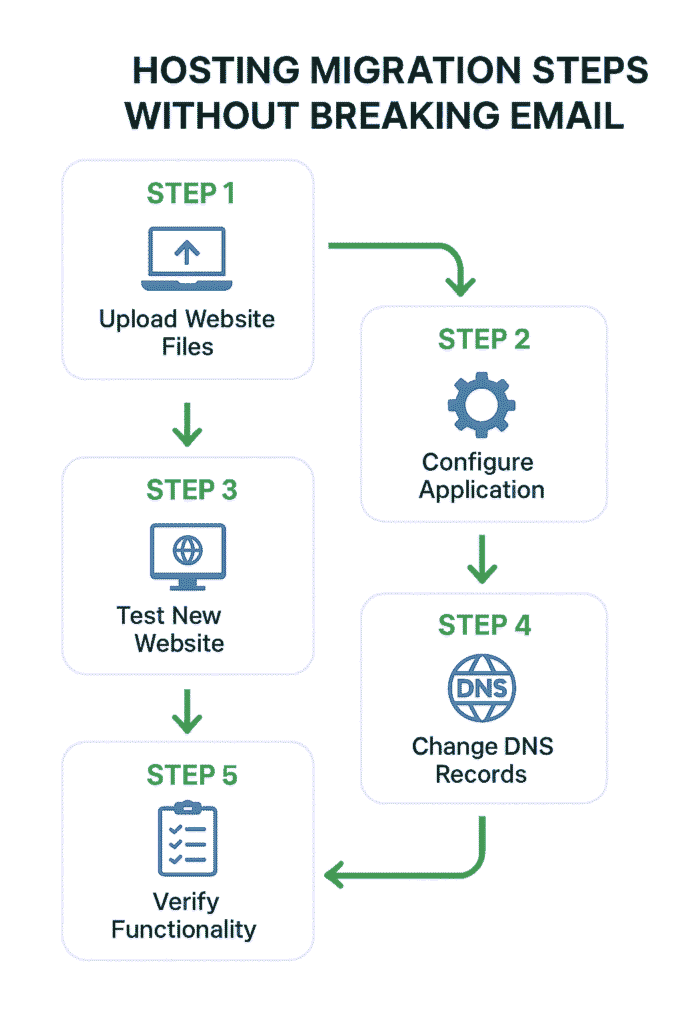
This is crucial for business clients. Follow this exact process:
Step 1 — Export all DNS records from old host
Copy:
- A
- CNAME
- MX
- TXT
- SRV
- AAAA
Step 2 — Recreate all DNS records at the new DNS host
Mirror everything exactly.
Step 3 — Only change the A record(s)
Your website moves, but your email stays untouched because MX values never changed.
Step 4 — If changing nameservers, recreate DNS zone before switching
Otherwise email will break.
Step 5 — Test before cutting over
Use:
nslookupdig- MXToolbox
To test propagation.
Final Thoughts
DNS is powerful, flexible, and foundational — but mistakes in DNS architecture can expose your real server IP, break email services, open security gaps, or cause downtime. Understanding the difference between TXT, A, CNAME, and NS records, knowing how subdomains and shared IPs work, and properly structuring hosting migrations are essential skills for every security engineer, DevOps engineer, and penetration tester.
With proper DNS hygiene, Cloudflare/WAF protection, and a clear understanding of how traffic flows, you can secure your web infrastructure while smoothly routing your domains, subdomains, and hosted services.



